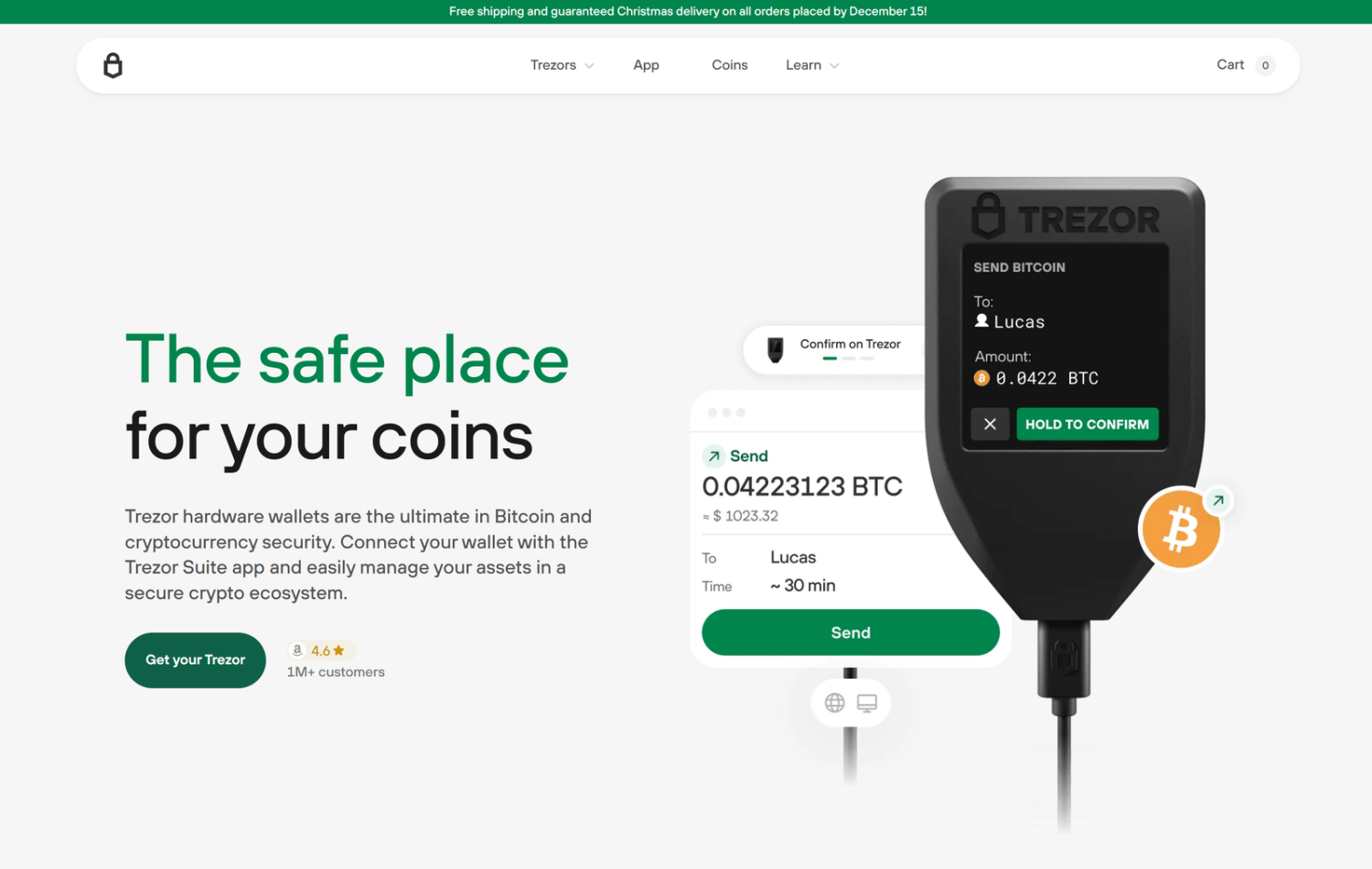
Trezor.io/start & Trezor Login – Complete Guide to Secure Crypto Access 🔐
Introduction
In today’s digital economy, protecting your cryptocurrency is more important than ever. With increasing cyber threats, relying on secure tools like Trezor.io/start and Trezor Login has become essential for crypto users. These solutions provide advanced protection by combining hardware wallet security with safe authentication methods.
This SEO-optimized guide explains how Trezor.io/start and Trezor Login work, their benefits, setup process, and best practices to keep your assets safe.
What is Trezor.io/start?
Trezor.io/start is the official onboarding page for setting up your Trezor hardware wallet. It ensures users follow the correct steps to initialize their device safely and avoid phishing risks.
By using Trezor.io/start, you can:
-
Install Trezor Suite securely
-
Set up your hardware wallet
-
Generate and back up your recovery seed
-
Configure PIN protection
It acts as the foundation of your crypto security journey.
What is Trezor Login?
Trezor Login is a secure authentication method that allows users to access their wallets and supported services using their Trezor device. Instead of relying on passwords, Trezor Login requires physical confirmation on the device.
This ensures:
-
Private keys remain offline
-
Unauthorized access is prevented
-
Phishing attacks are minimized
Together, Trezor.io/start and Trezor Login create a complete security ecosystem.
How to Set Up Using Trezor.io/start
Follow these steps to get started:
1. Visit Official Website
Go to Trezor.io/start and ensure the URL is correct.
2. Connect Your Device
Plug in your Trezor hardware wallet via USB.
3. Install Trezor Suite
Download the official application for managing your wallet.
4. Install Firmware
Update or install firmware for optimal performance.
5. Create Wallet
Generate a new wallet and receive your recovery seed phrase.
6. Backup Seed Phrase
Write it down and store it offline securely.
7. Set PIN
Add a strong PIN for device protection.
After completing these steps, your wallet is ready for use with Trezor Login.
How Trezor Login Works
Using Trezor Login is simple and secure:
-
Connect your Trezor device
-
Open Trezor Suite or supported platform
-
Enter your PIN
-
Confirm login on the device screen
-
Access your wallet safely
Every login requires physical approval, making Trezor Login highly secure.
Key Features
1. Offline Security
Both Trezor.io/start and Trezor Login ensure your private keys never leave the device.
2. Multi-Currency Support
Manage Bitcoin, Ethereum, and many other cryptocurrencies.
3. User-Friendly Interface
Trezor Suite provides an easy and intuitive dashboard.
4. Secure Transactions
All transactions must be verified on the hardware device.
5. Open-Source Technology
Transparent and trusted by the crypto community.
Benefits of Using Trezor.io/start & Trezor Login
-
Maximum Security 🔒 – Hardware-based protection
-
No Password Risks – Eliminates weak password issues
-
Phishing Protection – Only official device confirmations
-
Full Control – You own your private keys
-
Reliable Backup – Recovery seed ensures access
These features make Trezor.io/start and Trezor Login ideal for both beginners and professionals.
Best Security Practices
To stay safe while using Trezor.io/start and Trezor Login, follow these tips:
-
Always access the official website
-
Never share your recovery seed
-
Store backup phrases offline
-
Keep firmware updated
-
Avoid public or unsecured devices
Security depends on both technology and user awareness.
Common Issues & Fixes
Device Not Detected
-
Change USB cable or port
-
Restart your system
Forgot PIN
-
Reset device and recover using seed phrase
Login Errors
-
Update Trezor Suite and firmware
Who Should Use Trezor?
-
Long-term crypto investors
-
Traders managing multiple assets
-
Beginners seeking secure storage
-
Anyone concerned about hacking risks
Using Trezor.io/start and Trezor Login ensures your assets are always protected.
Conclusion
Trezor.io/start and Trezor Login are essential tools for anyone serious about crypto security. From initial setup to daily access, they provide unmatched protection through hardware-based authentication.
By following the correct setup process and security practices, you can confidently manage your digital assets without fear of cyber threats.
FAQs
1. Is Trezor.io/start safe?
Yes, it is the official and secure setup page for Trezor devices.
2. What is Trezor Login used for?
It is used for secure authentication and wallet access.
3. Can I recover my wallet if I lose my device?
Yes, using your recovery seed phrase.
4. Does Trezor support multiple coins?
Yes, it supports a wide range of cryptocurrencies.
5. Is Trezor suitable for beginners?
Absolutely! Both Trezor.io/start and Trezor Login are easy to use.